Root your Phone with just 1-Click
Today I read that someone demoed how to put rootkit into your phone during the Defcon. But there are no details, the keywords like kernel moudle, install apk, remote phone call, …, all reminds me the old phishing attack. Then I thought, can it be the trick used to root Droid X?
Actually this exploid works on almost every Android phone because it leverages a vulnerability in the framework. XDA developers also confirmed the success on various N1 model. But can it be used on real attack?
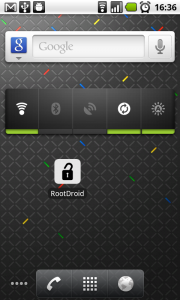
To demonstrate how dangerous the local exploit is, I wrote an Android application that inject the su program into your phone. With Superuser.apk you can gain root access whenever you run su from adb shell.
No additional permissions required! This works on my stock Nexus One and in theory any Android. Just one click I can root you phone (optionally take away your data simultaneously). Don’t trust me or any other similar programs floating around the market, or simply don’t install any program until your carrier fix this.
Download the apk here: http://0xlab.org/~kanru/RootDroid-release.apkmd5: 20894acd3be808c51ce32491872ba027 sha1: 889fc92692c0e58e83673dedbabbc66d5c6318b1
This vulnerability has been fixed in CyanogenMod two weeks ago, and the source code is landing the AOSP froyo branch, but there is still no official fix update from Google. Consider how dangerous this is, I may not install any third party application until an OTA arrives or just go ahead with a customized rom with my newly rooted phone ;-)